Ddos Attack Tool, Anonymous Releases A Ddos Tool To Attack Websites
A 2018 attack on GitHub is said to be the biggest DDoS attack to date. It doesnt affect other services and ports on the target network.
Ddos Attacks What They Are And How To Ddos Pluralsight
Buffer Overflow Attack with Example.

Ddos attack tool. Ways to place K bishops on an NN chessboard. A DoS or DDoS attack is analogous to a group of people crowding the entry door of a shop making it hard for legitimate customers to enter thus disrupting trade. This botnet or group of hijacked systems is used to launch the attack all together against a single target at the same time.
15 Mar 21. This tool can be used to flood a victims network with multiple UDP packets. This software is provided by the copyright holder or contributors as is and any express or implied warranties including but not limited to the implied warranties of merchantability and fitness for a particular purpose are disclaimed.
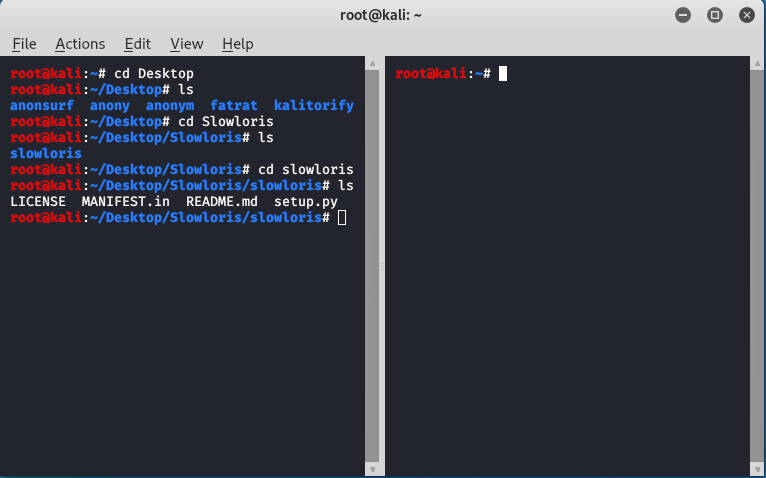
However this test will be very limited in scale and the types of attack traffic used. Slowloris tool is used to make a DDoS attack. Denial of Service DoS.
It is used to make the server down. This tool is. It achieves this by sending a partial request.
It is distinct from other denial of service DoS attacks in that it uses a single Internet-connected device one network connection to flood a target with malicious traffic. Path Traversal Attack and Prevention. In a distributed denial-of-service attack DDoS attack the incoming traffic flooding the victim originates from many different sources.
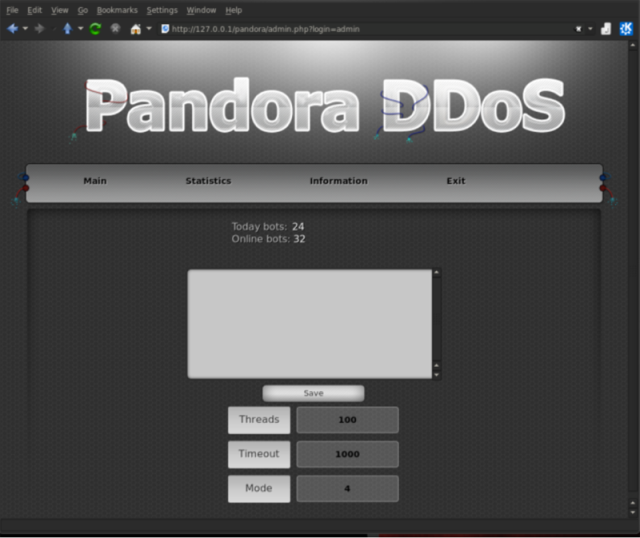
Simulate a basic DDoS attack on your network and see how your defenses hold up. How to Detect ARP Spoof Attack using Scapy in Python. The attack is distributed because one attacker can handle 1000 bots.
The attack sent massive amounts of traffic to the platform which is used by millions of developers to post and share code. In no event. 0 This Week Last Update.
This massive DDoS attack took large sections of a countrys internet offline. A DDoS attack consists of a website being flooded by requests during a short period of time with the aim of overwhelming the site and causing it to crash. The Imperva DDoS protection tool keeps the entire network safe and shielded from attack by using high-capacity packet processing.
Panoptis plans to create a network security tool N-IDS to detect and block DoS and DDoS attacks. DDoS attacks achieve effectiveness using multiple compromised computer systems as a source of attack traffic. The distributed element means that these attacks are coming from multiple locations at the same time as compared to a DoS which comes from just one location.
How to Perform a. This tool is used for IP spoofing and opening the TCP connections. This effectively makes it impossible to stop the attack simply by blocking a single source.
A DDoS attack is launched from numerous compromised devices often distributed globally in what is referred to as a botnet. With a patent-protected real-time signature creation technology DefensePro is a DDoS defense device that can automatically generate DDoS prevention and protection for zero-day and unknown attacks. It will only give you a taste of how to prepare for a real Internet-scale attack.
This nuance is the main reason for the existence of these two somewhat different definitions. It tries to hold the connections as long as possible. Usually DDoS attacks focus on generating attacks that manipulate the default or even proper workings of network equipment and services eg routers naming services or caching services.
What is a SSDP DDoS Attack. Search engines may include computers and other network. A multi-vector DDoS attack uses multiple attack pathways in order to overwhelm a target in different ways potentially distracting mitigation efforts on any one trajectory.
Use on your own risk. The main downside of the Imperva tool is that it is limited to DDoS attack. It provides either always-on or on-demand DDoS protection depending on what suits your business most and also includes automatically updating dashboards that show attack traffic details.
This attack tries to keep the maximum connection engaged with those that are open. DDoS attacks are a complex form of denial-of-service DoS attacks which only come from one source. Für Verweigerung des Dienstes bezeichnet in der Informationstechnik die Nichtverfügbarkeit eines Internetdienstes der eigentlich verfügbar sein sollteHäufigster Grund ist die Überlastung des DatennetzesDas kann unbeabsichtigt verursacht werden oder durch einen konzertierten Angriff auf die Server oder sonstige Komponenten des Datennetzes erfolgen.
A Simple Service Discovery Protocol SSDP attack is a reflection-based distributed denial-of-service DDoS attack that exploits Universal Plug and Play UPnP networking protocols in order to send an amplified amount of traffic to a targeted victim overwhelming the targets infrastructure and taking their web resource offline. A distributed denial-of-service DDoS attack is a type of cyberattack that uses the distributed power of many compromised machines to flood the target system with requests overwhelming the system and preventing it from functioning. In fact thats the main problem.
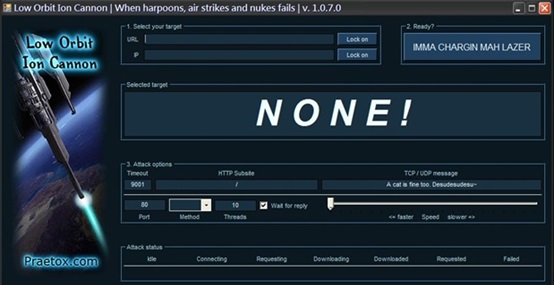
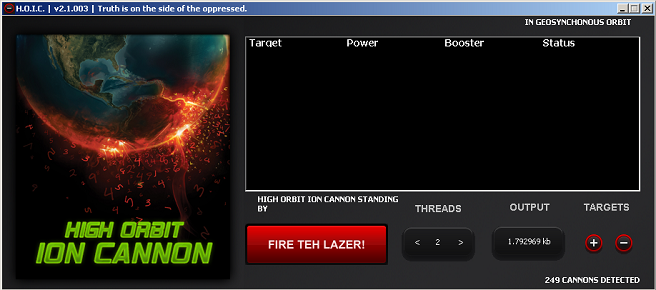
In this section we will use an open source tool called Kali Linux to create a simplified simulation of a DDoS attack. A Distributable Denied-of-Service DDOS attack server that cuts off targets or surrounding infrastructure in a flood of Internet traffic. Loic - ddos-attack tool.
Slowloris DDOS Attack Tool in Kali Linux. More than 200 organisations across Belgium including the government and parliament were affected by a DDoS attack. The DDoS Attack Defender Tool is a simple yet effective python script that defends your linux system against a distributed denial of service DDoS attack by limiting the number of connections per IP Address.
Goldeneye DDos Tool in Kali Linux. A new powerfull stable version of low orbit ion cannon disclaimer. It sends authorized HTTP traffic to the server.
Distributed denial-of-service DDoS attack is a kind of DoS attack in which the attacker levarges a group of remote systems that are compromised and under the attackers control. A DDoS attack occurs when a threat actor uses resources from multiple remote locations to attack an organizations online operations. If your site suffers a DDoS attack you will receive thousands of requests.
An attack that targets multiple layers of the protocol stack at the same time such as a DNS amplification targeting layers 34 coupled with an HTTP flood targeting layer 7 is an example of multi-vector DDoS. Within 18 seconds DefensePro can detect characterize and generate an optimal signature to block unknown attacks with a minimal false. If you are curious to know how to perform a DDoS attack and bring down any website keep reading this article as in this article a step-by-step method is given to perform a DDoS attack using the command prompt CMD.
DDoS-Ripper What is a DDoS Attack. Automated Zero-Day DDoS Attack Protection.
Github M57 Ardt Akamai Reflective Ddos Tool Attack The Origin Host Behind The Akamai Edge Hosts And Ddos Protection Offered By Akamai Services

Student Makes X4u Doser Ddos Tool Available Link11

8 Best Ddos Attack Tools Free Ddos Tool Of The Year 2021
Ddos Attacks And Mitigation Nsfocus Inc A Global Network And Cyber Security Leader Protects Enterprises And Carriers From Advanced Cyber Attacks
Slowloris Ddos Attack Tool In Kali Linux Geeksforgeeks

Legitimate Test Tool Or Ddos Attack Weapon Corero Network Security Corero
Github Ha3mrx Ddos Attack Ddos Attack Is A Python Script Online Attack

Thanks To Anonymous Latest Toolset Anyone Can Play The Ddos Game

8 Best Ddos Attack Tools Free Ddos Tool Of The Year 2021
White Hats Publish Ddos Hijacking Manual Turn Tables On Attackers Ars Technica
What Is A Dos Ddos Attack Script Or Toolkit Ddos Tools Imperva

8 Best Ddos Attack Tools Free Ddos Tool Of The Year 2021
Ddos Attacks What They Are And How To Ddos Pluralsight
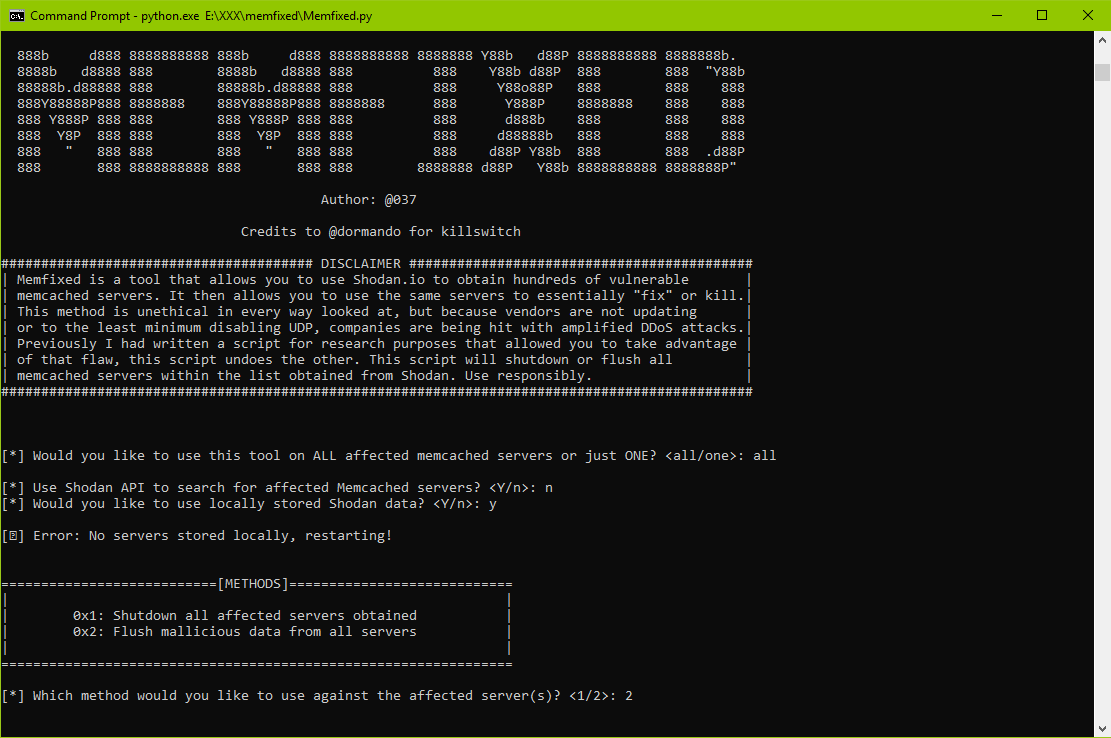
Memfixed Tool Helps Mitigate Memcached Based Ddos Attacks

Anonymous Releases A Ddos Tool To Attack Websites

Understanding Dos Attacks And The Best Free Dos Attacking Tools Updated In 2020 Infosec Resources

Bluebook A Ddos Attack Tool Secret Hacker Official
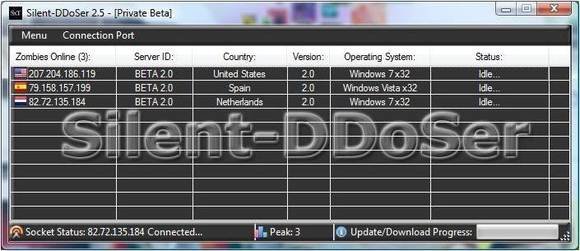
Silent Ddoser Five Ddos Attack Tools That You Should Know About

Thanks To Anonymous Latest Toolset Anyone Can Play The Ddos Game